PicoCTF Crypto Challenges#
PicoCTF Challenge: Mod26#
Cryptography can be easy, do you know what ROT13 is?
cvpbPGS{arkg_gvzr_V'yy_gel_2_ebhaqf_bs_ebg13_uJdSftmh}
from string import ascii_lowercase as alphabet
def rot(given: str, n: int) -> str:
"""
Passes anything that is not lowercase ascii
"""
return "".join(
[
alphabet[(alphabet.index(letter.lower()) + n) % 26]
if letter.lower() in alphabet
else letter
for letter in given
]
)
given = "cvpbPGS{arkg_gvzr_V'yy_gel_2_ebhaqf_bs_ebg13_uJdSftmh}"
rot(given, 13)
"picoctf{next_time_i'll_try_2_rounds_of_rot13_hwqfsgzu}"
PicoCTF Challenge: The Numbers#
https://play.picoctf.org/practice/challenge/68?category=2&page=1
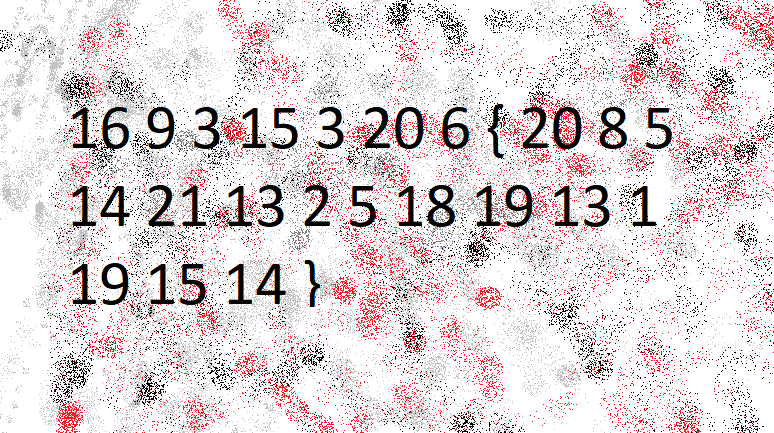
numbers = [
16,
9,
3,
15,
3,
20,
6,
"{",
20,
8,
5,
14,
21,
13,
2,
5,
18,
19,
13,
1,
19,
15,
14,
"}",
]
"".join([alphabet[number - 1] if type(number) is int else number for number in numbers])
'picoctf{thenumbersmason}'
PicoCTF Challenge: No Padding, No Problem#
Welcome to the Padding Oracle Challenge This oracle will take anything you give it and decrypt using RSA. It will not accept the ciphertext with the secret message… Good Luck!
n = 120199559973193838354549892082142658207097650252359537516083460817553570005386613360986166000912493892791691164047531246715465233526804393369018699102692997585282405404929642411769685589191403004314951464004606040856090582644697868607882790061040095046085624676496925724241831512872034324551286084224297842637
e = 65537
c = 7663878604603605176178448503196010884137598661534924550657029084967288918950468353300685296575323894095255258617919415054374805989359325652736220230210866108008415526260085801082953500312514266232101295493572110042773495662486665996281526563951110999276024750039987398638060394996693137783011654264697917058
RSA is malleable (Paar 192). We can transform the ciphertext into another ciphertext which is a known transformation of the plaintext… This can be achieved in RSA if the attacker replaces the ciphertext y with (s**e)*y with an integer s. For this example, we’ll double the cipher text (and know that we have to half the result returned from the oracle).
x = c * (pow(2, e, n))
Give x to Oracle and receive doubled
doubled = 580550060391700078946913236734911770139931497702556153513487440893406629034802718534645538074938502890768853279675297196794
result = int(doubled // 2)
print(result)
290275030195850039473456618367455885069965748851278076756743720446703314517401359267322769037469251445384426639837648598397
bytearray.fromhex(format(result, 'x')).decode()
'picoCTF{m4yb3_Th0se_m3s54g3s_4r3_difurrent_1772735}'